

A number of safety vulnerabilities have been disclosed within the TCP/IP community protocol stack of an open-source reference implementation of the Unified Extensible Firmware Interface (UEFI) specification used broadly in fashionable computer systems.
Collectively dubbed PixieFail by Quarkslab, the 9 points reside within the TianoCore EFI Growth Package II (EDK II) and may very well be exploited to realize distant code execution, denial-of-service (DoS), DNS cache poisoning, and leakage of delicate data.
UEFI firmware – which is liable for booting the working system – from AMI, Intel, Insyde, and Phoenix Applied sciences are impacted by the shortcomings.
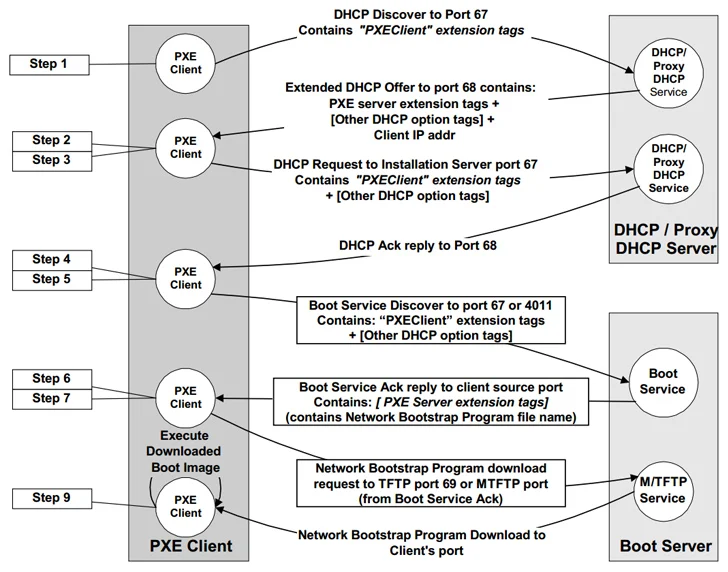
EDK II incorporates its personal TCP/IP stack referred to as NetworkPkg to allow community functionalities accessible throughout the preliminary Preboot eXecution Setting (PXE, pronounced “pixie”) stage, which permits for administration duties within the absence of a working working system.
In different phrases, it’s a client-server interface besides a tool from its community interface card (NIC) and permits networked computer systems that aren’t but loaded with an working system to be configured and booted remotely by an administrator.
The code to PXE is included as a part of the UEFI firmware on the motherboard or throughout the NIC firmware read-only reminiscence (ROM).
The problems recognized by Quarkslab throughout the EDKII’s NetworkPkg embody overflow bugs, out-of-bounds learn, infinite loops, and the usage of weak pseudorandom quantity generator (PRNG) that end in DNS and DHCP poisoning assaults, data leakage, denial of service, and knowledge insertion assaults on the IPv4 and IPv6 layer.
The checklist of flaws is as follows –
- CVE-2023-45229 (CVSS rating: 6.5) – Integer underflow when processing IA_NA/IA_TA choices in a DHCPv6 Promote message
- CVE-2023-45230 (CVSS rating: 8.3) – Buffer overflow within the DHCPv6 shopper by way of a protracted Server ID choice
- CVE-2023-45231 (CVSS rating: 6.5) – Out-of-bounds learn when dealing with a ND Redirect message with truncated choices
- CVE-2023-45232 (CVSS rating: 7.5) – Infinite loop when parsing unknown choices within the Vacation spot Choices header
- CVE-2023-45233 (CVSS rating: 7.5) – Infinite loop when parsing a PadN choice within the Vacation spot Choices header
- CVE-2023-45234 (CVSS rating: 8.3) – Buffer overflow when processing DNS Servers choice in a DHCPv6 Promote message
- CVE-2023-45235 (CVSS rating: 8.3) – Buffer overflow when dealing with Server ID choice from a DHCPv6 proxy Promote message
- CVE-2023-45236 (CVSS rating: 5.8) – Predictable TCP Preliminary Sequence Numbers
- CVE-2023-45237 (CVSS rating: 5.3) – Use of a weak pseudorandom quantity generator
“The affect and exploitability of those vulnerabilities depend upon the precise firmware construct and the default PXE boot configuration,” the CERT Coordination Middle (CERT/CC) stated in an advisory.
“An attacker throughout the native community (and, in sure eventualities remotely) may exploit these weaknesses to execute distant code, provoke DoS assaults, conduct DNS cache poisoning, or extract delicate data.”
