
Cybersecurity researchers have disclosed a safety flaw within the Opera internet browser for Microsoft Home windows and Apple macOS that could possibly be exploited to execute any file on the underlying working system.
The distant code execution vulnerability has been codenamed MyFlaw by the Guardio Labs analysis crew owing to the truth that it takes benefit of a function known as My Circulate that makes it potential to sync messages and recordsdata between cell and desktop units.
“That is achieved via a managed browser extension, successfully bypassing the browser’s sandbox and the whole browser course of,” the corporate stated in a press release shared with The Hacker Information.
The difficulty impacts each the Opera browser and Opera GX. Following accountable disclosure on November 17, 2023, it was addressed as a part of updates shipped on November 22, 2023.
My Circulate contains a chat-like interface to alternate notes and recordsdata, the latter of which may be opened by way of an internet interface, that means a file may be executed outdoors of the browser’s safety boundaries.
It’s pre-installed within the browser and facilitated via a built-in (or inner) browser extension known as “Opera Contact Background,” which is liable for speaking with its cell counterpart.
This additionally signifies that the extension comes with its personal manifest file specifying all of the required permissions and its conduct, together with a property generally known as externally_connectable that declares which different internet pages and extensions can hook up with it.
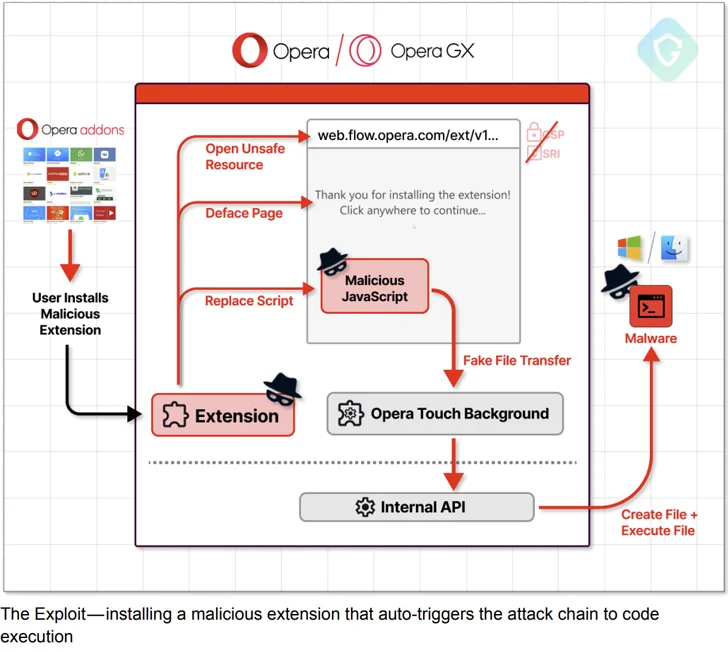
Within the case of Opera, the domains that may discuss to the extension ought to match the patterns “*.stream.opera.com” and “.stream.op-test.internet” – each managed by the browser vendor itself.
“This exposes the messaging API to any web page that matches the URL patterns you specify,” Google notes in its documentation. “The URL sample should include no less than a second-level area.”
Guardio Labs stated it was capable of unearth a “long-forgotten” model of the My Circulate touchdown web page hosted on the area “internet.stream.opera.com” utilizing the urlscan.io web site scanner software.

“The web page itself seems fairly the identical as the present one in manufacturing, however adjustments lie below the hood: Not solely that it lacks the [content security policy] meta tag, but it surely additionally holds a script tag calling for a JavaScript file with none integrity test,” the corporate stated.
“That is precisely what an attacker wants – an unsafe, forgotten, weak to code injection asset, and most significantly, has entry to (very) excessive permission native browser API.”
The assault chain then hinges, making a specifically crafted extension that masquerades as a cell gadget to pair with the sufferer’s laptop and transmit an encrypted malicious payload by way of the modified JavaScript file to the host for subsequent execution by prompting the consumer to click on wherever on the display.
The findings spotlight the growing complexity of browser-based assaults and the totally different vectors that may be exploited by menace actors to their benefit.
“Regardless of working in sandboxed environments, extensions may be highly effective instruments for hackers, enabling them to steal data and breach browser safety boundaries,” the corporate advised The Hacker Information.
“This underscores the necessity for inner design adjustments at Opera and enhancements in Chromium’s infrastructure. For example, disabling third-party extension permissions on devoted manufacturing domains, just like Chrome’s internet retailer, is advisable however has not but been carried out by Opera.”
When reached for remark, Opera stated it moved rapidly to shut the safety gap and implement a repair on the server facet and that it is taking steps to stop such points from taking place once more.
“Our present construction makes use of an HTML customary, and is the most secure choice that doesn’t break key performance,” the corporate stated. “After Guardio alerted us to this vulnerability, we eliminated the reason for these points and we’re ensuring that related issues won’t seem sooner or later.”
“We want to thank Guardio Labs for his or her work on uncovering and instantly alerting us to this vulnerability. This collaboration demonstrates how we work along with safety specialists and researchers all over the world to enrich our personal efforts at sustaining and bettering the safety of our merchandise and guaranteeing our customers have a protected on-line expertise.”
