Menace actors have been exploiting the newly disclosed zero-day flaw in Palo Alto Networks PAN-OS software program courting again to March 26, 2024, almost three weeks earlier than it got here to gentle yesterday.
The community safety firm’s Unit 42 division is monitoring the exercise beneath the title Operation MidnightEclipse, attributing it because the work of a single menace actor of unknown provenance.
The safety vulnerability, tracked as CVE-2024-3400 (CVSS rating: 10.0), is a command injection flaw that allows unauthenticated attackers to execute arbitrary code with root privileges on the firewall.
It is value noting that the difficulty is relevant solely to PAN-OS 10.2, PAN-OS 11.0, and PAN-OS 11.1 firewall configurations which have GlobalProtect gateway and system telemetry enabled.
Operation MidnightEclipse entails the exploitation of the flaw to create a cron job that runs each minute to fetch instructions hosted on an exterior server (“172.233.228[.]93/coverage” or “172.233.228[.]93/patch”), that are then executed utilizing the bash shell.
The attackers are stated to have manually managed an entry management listing (ACL) for the command-and-control (C2) server to make sure that it will possibly solely be accessed from the system speaking with it.

Whereas the precise nature of the command is unknown, it is suspected that the URL serves as a supply car for a Python-based backdoor on the firewall that Volexity – which found in-the-wild exploitation of CVE-2024-3400 on April 10, 2024 – is monitoring as UPSTYLE and is hosted on a unique server (“144.172.79[.]92” and “nhdata.s3-us-west-2.amazonaws[.]com”).
The Python file is designed to jot down and launch one other Python script (“system.pth”), which subsequently decodes and runs the embedded backdoor element that is accountable for executing the menace actor’s instructions in a file referred to as “sslvpn_ngx_error.log.” The outcomes of the operation are written to a separate file named “bootstrap.min.css.”
Probably the most fascinating facet of the assault chain is that each the information used to extract the instructions and write the outcomes are respectable information related to the firewall –
- /var/log/pan/sslvpn_ngx_error.log
- /var/appweb/sslvpndocs/global-protect/portal/css/bootstrap.min.css
As for a way the instructions are written to the net server error log, the menace actor forges specifically crafted community requests to a non-existent net web page containing a particular sample. The backdoor then parses the log file and searches for the road matching the identical common expression (“img[([a-zA-Z0-9+/=]+)]”) to decode and run the command inside it.
“The script will then create one other thread that runs a perform referred to as restore,” Unit 42 stated. “The restore perform takes the unique content material of the bootstrap.min.css file, in addition to the unique entry and modified instances, sleeps for 15 seconds and writes the unique contents again to the file and units the entry and modified instances to their originals.”
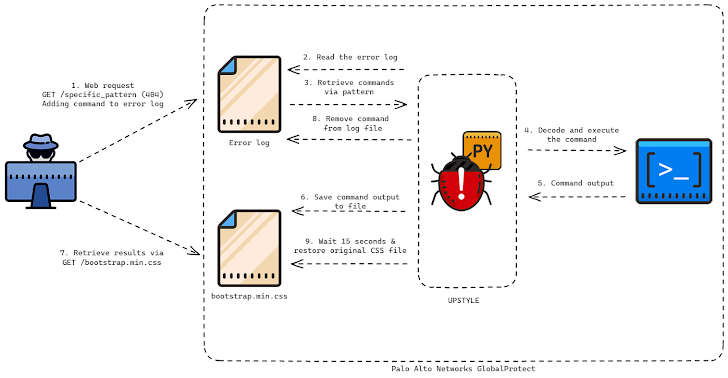
The primary purpose seems to be to keep away from leaving traces of the command outputs, necessitating that the outcomes are exfiltrated inside 15 seconds earlier than the file is overwritten.
Volexity, in its personal evaluation, stated it noticed the menace actor remotely exploiting the firewall to create a reverse shell, obtain extra tooling, pivot into inner networks, and in the end exfiltrate knowledge. The precise scale of the marketing campaign is presently unclear. The adversary has been assigned the moniker UTA0218 by the corporate.

“The tradecraft and velocity employed by the attacker suggests a extremely succesful menace actor with a transparent playbook of what to entry to additional their goals,” the American cybersecurity agency stated.
“UTA0218’s preliminary goals have been aimed toward grabbing the area backup DPAPI keys and focusing on energetic listing credentials by acquiring the NTDS.DIT file. They additional focused consumer workstations to steal saved cookies and login knowledge, together with the customers’ DPAPI keys.”
Organizations are advisable to search for indicators of lateral motion internally from their Palo Alto Networks GlobalProtect firewall system.
The event has additionally prompted the U.S. Cybersecurity and Infrastructure Safety Company (CISA) so as to add the flaw to its Recognized Exploited Vulnerabilities (KEV) catalog, requiring federal businesses to use the patches by April 19 to mitigate potential threats. Palo Alto Networks is anticipated to launch fixes for the flaw no later than April 14.
“Concentrating on edge units stays a well-liked vector of assault for succesful menace actors who’ve the time and sources to speculate into researching new vulnerabilities,” Volexity stated.
“It’s extremely seemingly UTA0218 is a state-backed menace actor based mostly on the sources required to develop and exploit a vulnerability of this nature, the kind of victims focused by this actor, and the capabilities displayed to put in the Python backdoor and additional entry sufferer networks.”