

Google on Tuesday mentioned it is piloting a brand new characteristic in Chrome referred to as System Sure Session Credentials (DBSC) to assist defend customers in opposition to session cookie theft by malware.
The prototype – at present examined in opposition to “some” Google Account customers operating Chrome Beta – is constructed with an goal to make it an open net normal, the tech large’s Chromium crew mentioned.
“By binding authentication classes to the machine, DBSC goals to disrupt the cookie theft business since exfiltrating these cookies will now not have any worth,” the corporate famous.
“We expect it will considerably scale back the success price of cookie theft malware. Attackers could be pressured to behave regionally on the machine, which makes on-device detection and cleanup simpler, each for anti-virus software program in addition to for enterprise managed gadgets.”
The event comes on the again of reviews that off-the-shelf data stealing malware are discovering methods to steal cookies in a way that permits risk actors to bypass multi-factor authentication (MFA) safety and acquire unauthorized entry to on-line accounts.

Such session hijacking strategies have been round for years. In October 2021, Google’s Menace Evaluation Group (TAG) detailed a phishing marketing campaign that focused YouTube content material creators with cookie stealing malware to hijack their accounts and monetize the entry for perpetrating cryptocurrency scams.
Earlier this January, CloudSEK revealed that data stealers like Lumma, Rhadamanthys, Stealc, Meduza, RisePro, and WhiteSnake have up to date their capabilities to hijack consumer classes and permit steady entry to Google companies even after a password reset.
Google advised The Hacker Information on the time that “assaults involving malware that steal cookies and tokens are usually not new; we routinely improve our defenses in opposition to such strategies and to safe customers who fall sufferer to malware.”
It additional really useful customers to allow Enhanced Protected Searching within the Chrome net browser to guard in opposition to phishing and malware downloads.
DBSC goals to chop down on such malicious efforts by introducing a cryptographic method that ties collectively the classes to the machine such that it makes it tougher for the adversaries to abuse the stolen cookies and hijack the accounts.
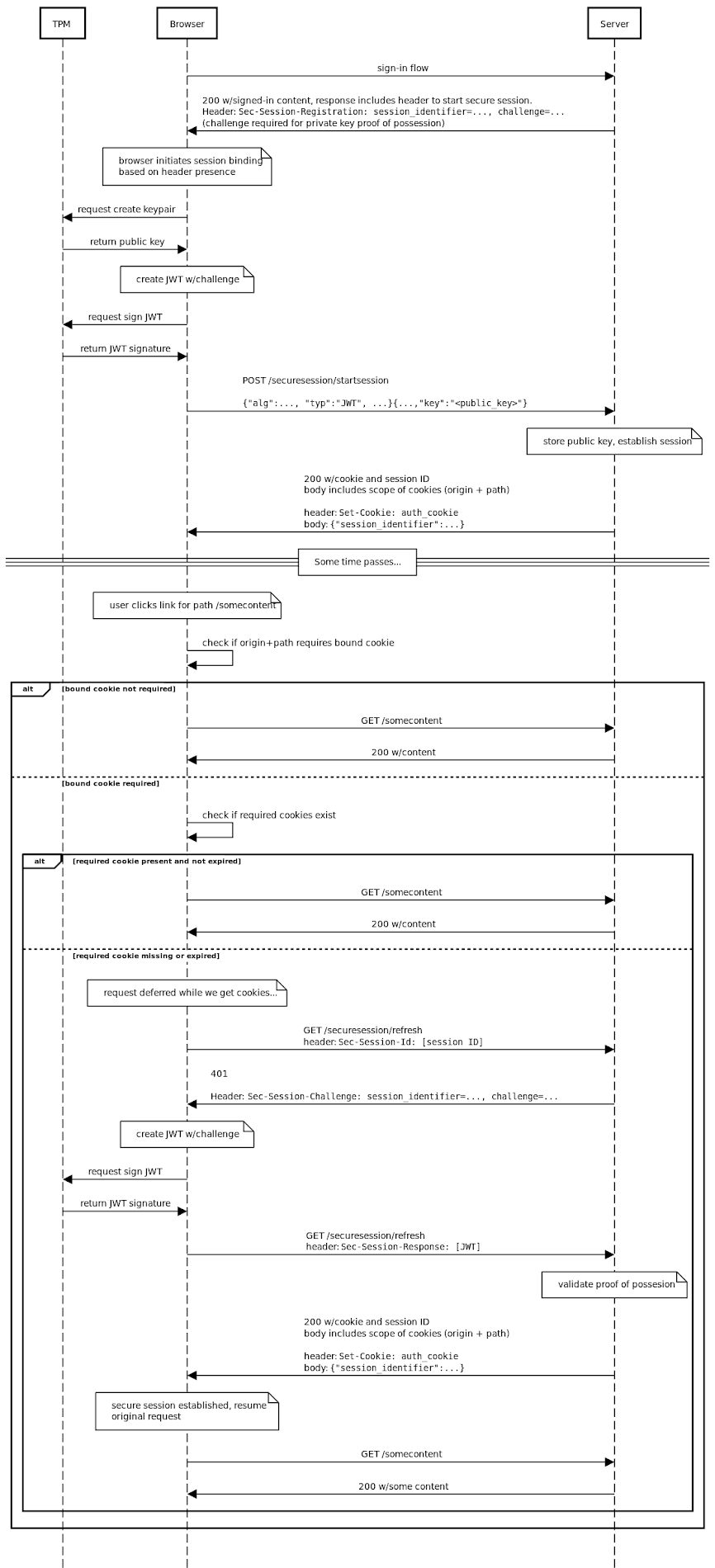
Provided through an API, the brand new characteristic achieves this by permitting a server to affiliate a session with a public key created by the browser as a part of a public/non-public key pair when a brand new session is launched.
It is value noting that the important thing pair is saved regionally on the machine utilizing Trusted Platform Modules (TPMs). As well as, the DBSCI API permits the server to confirm proof-of-possession of the non-public key all through the session lifetime to make sure the session is energetic on the identical machine.
“DBSC affords an API for web sites to regulate the lifetime of such keys, behind the abstraction of a session, and a protocol for periodically and robotically proving possession of these keys to the web site’s servers,” Google’s Kristian Monsen and Arnar Birgisson mentioned.
“There’s a separate key for every session, and it shouldn’t be doable to detect that two completely different session keys are from one machine. By device-binding the non-public key and with acceptable intervals of the proofs, the browser can restrict malware’s capacity to dump its abuse off of the consumer’s machine, considerably rising the possibility that both the browser or server can detect and mitigate cookie theft.”

One essential caveat is that DBSC banks on consumer gadgets having a safe approach of signing challenges whereas defending non-public keys from exfiltration by malware, necessitating that the net browser has entry to the TPM.
Google mentioned assist for DBSC can be initially rolled out to roughly half of Chrome’s desktop customers primarily based on the {hardware} capabilities of their machines. The most recent undertaking can also be anticipated to be in sync with the corporate’s broader plans to sundown third-party cookies within the browser by the tip of the yr through the Privateness Sandbox initiative.
“That is to make it possible for DBSC doesn’t change into a brand new monitoring vector as soon as third-party cookies are phased out, whereas additionally making certain that such cookies could be totally protected within the meantime,” it mentioned. “If the consumer utterly opts out of cookies, third-party cookies, or cookies for a selected web site, it will disable DBSC in these eventualities as nicely.”
The corporate additional famous that it is partaking with a number of server suppliers, identification suppliers (IdPs), and browser distributors like Microsoft Edge and Okta, who’ve expressed curiosity in DBSC. Origin trials for DBSC for all supported web sites are set to begin by the tip of the yr.
