Bogus installers for Adobe Acrobat Reader are getting used to distribute a brand new multi-functional malware dubbed Byakugan.
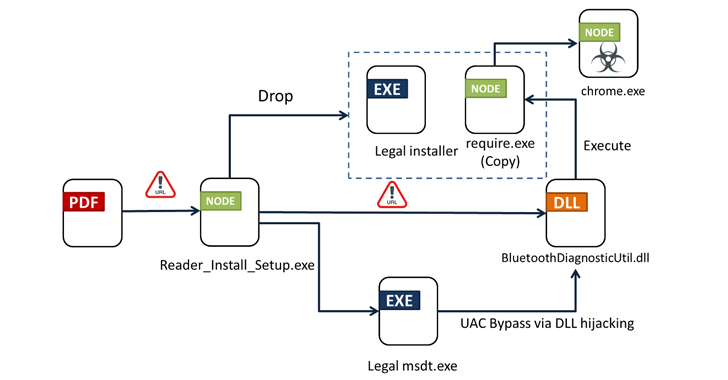
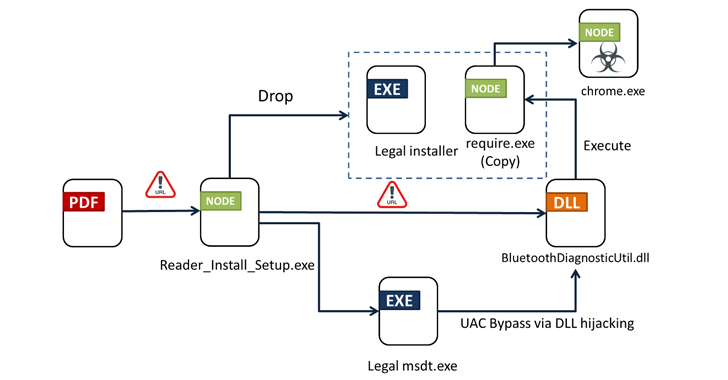
The place to begin of the assault is a PDF file written in Portuguese that, when opened, exhibits a blurred picture and asks the sufferer to click on on a hyperlink to obtain the Reader software to view the content material.
In keeping with Fortinet FortiGuard Labs, clicking the URL results in the supply of an installer (“Reader_Install_Setup.exe”) that prompts the an infection sequence. Particulars of the marketing campaign had been first disclosed by the AhnLab Safety Intelligence Heart (ASEC) final month.
The assault chain leverages strategies like DLL hijacking and Home windows Consumer Entry Management (UAC) bypass to load a malicious dynamic-link library (DLL) file named “BluetoothDiagnosticUtil.dll,” which, in flip, hundreds unleashes the ultimate payload. It additionally deploys a reputable installer for a PDF reader like Wondershare PDFelement.
The binary is supplied to assemble and exfiltrate system metadata to a command-and-control (C2) server and drop the primary module (“chrome.exe”) from a unique server that additionally acts as its C2 for receiving information and instructions.
“Byakugan is a node.js-based malware packed into its executable by pkg,” safety researcher Pei Han Liao mentioned. “Along with the primary script, there are a number of libraries similar to options.”

This contains organising persistence, monitoring the sufferer’s desktop utilizing OBS Studio, capturing screenshots, downloading cryptocurrency miners, logging keystrokes, enumerating and importing information, and grabbing information saved in internet browsers.
“There’s a rising pattern to make use of each clear and malicious elements in malware, and Byakugan isn’t any exception,” Fortinet mentioned. “This method will increase the quantity of noise generated throughout evaluation, making correct detections harder.”
The disclosure comes as ASEC revealed a brand new marketing campaign that propagates the Rhadamanthys data stealer beneath the guise of an installer for groupware.
“The risk actor created a faux web site to resemble the unique web site and uncovered the location to the customers utilizing the advert characteristic in engines like google,” the South Korean cybersecurity agency mentioned. “The malware in distribution makes use of the oblique syscall method to cover from the eyes of safety options.”
It additionally follows a discovery {that a} manipulated model of Notepad++ is being employed by unidentified risk actors to propagate the WikiLoader malware (aka WailingCrab).