
A DarkGate malware marketing campaign noticed in mid-January 2024 leveraged a just lately patched safety flaw in Microsoft Home windows as a zero-day utilizing bogus software program installers.
“Throughout this marketing campaign, customers have been lured utilizing PDFs that contained Google DoubleClick Digital Advertising (DDM) open redirects that led unsuspecting victims to compromised websites internet hosting the Microsoft Home windows SmartScreen bypass CVE-2024-21412 that led to malicious Microsoft (.MSI) installers,” Development Micro stated.
CVE-2024-21412 (CVSS rating: 8.1) issues an web shortcut recordsdata safety characteristic bypass vulnerability that allows an unauthenticated attacker to bypass SmartScreen protections by tricking a sufferer into clicking on a specifically crafted file.
It was fastened by Microsoft as a part of its Patch Tuesday updates for February 2024, however not earlier than it was weaponized by a risk actor referred to as Water Hydra (aka DarkCasino) to ship the DarkMe malware in assaults concentrating on monetary establishments.
The newest findings from Development Micro present that the vulnerability has come underneath broader exploitation than beforehand thought, with the DarkGate marketing campaign leveraging it along with open redirects from Google Adverts to proliferate the malware.
The subtle assault chain begins with victims clicking on a hyperlink embedded inside a PDF attachment despatched through a phishing electronic mail. The hyperlink deploys an open redirect from Google’s doubleclick[.]internet area to a compromised internet server internet hosting a malicious .URL web shortcut file that exploits CVE-2024-21412.
Particularly, the open redirects are designed to distribute pretend Microsoft software program installers (.MSI) masquerading as professional software program, comparable to Apple iTunes, Notion, NVIDIA, which come fitted with a side-loaded DLL file that decrypted and contaminated customers with DarkGate (model 6.1.7).
It is value noting that one other now-fixed bypass flaw in Home windows SmartScreen (CVE-2023-36025, CVSS rating: 8.8) has been employed by risk actors to ship DarkGate, Phemedrone Stealer, and Mispadu over the previous few months.
The abuse of Google Adverts applied sciences permits risk actors to extend the attain and scale of their assaults via totally different advert campaigns which might be tailor-made for particular audiences.
“Utilizing pretend software program installers, together with open redirects, is a potent mixture and may result in many infections,” safety researchers Peter Girnus, Aliakbar Zahravi, and Simon Zuckerbraun stated. “It’s important to stay vigilant and to instruct customers to not belief any software program installer that they obtain outdoors of official channels.”
The event comes because the AhnLab Safety Intelligence Heart (ASEC) and eSentire revealed that counterfeit installers for Adobe Reader, Notion and Synaptics are being distributed through pretend PDF recordsdata and seemingly professional web sites to deploy info stealers like LummaC2 and the XRed backdoor.
It additionally follows the invention of latest stealer malware households like Planet Stealer, Rage Stealer (aka xStealer), and Tweaks (aka Tweaker), including to the plethora of cyber threats which might be able to harvesting delicate info from compromised hosts.
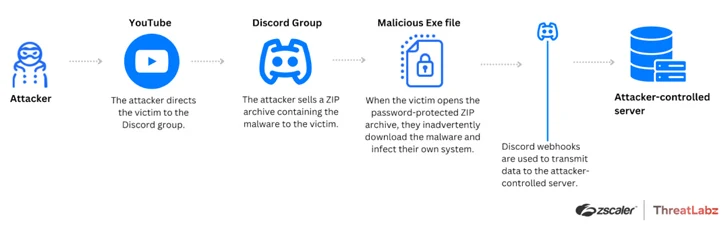
“Attackers are exploiting in style platforms, like YouTube and Discord, to distribute Tweaks to Roblox customers, capitalizing on the flexibility of professional platforms to evade detection by internet filter block lists that sometimes block identified malicious servers,” Zscaler ThreatLabz stated.
“Attackers share malicious recordsdata disguised as Frames Per Second (FPS) optimization packages with customers and, in flip, customers infect their very own methods with Tweaks malware.”
The PowerShell-based stealer is supplied to exfiltrate delicate knowledge, together with consumer info, location, Wi-Fi profiles, passwords, Roblox IDs, and in-game foreign money particulars, to an attacker-controlled server through a Discord webhook.
Malvertising and social engineering campaigns have additionally been noticed performing as an preliminary entry vector to disseminate a variety of stealer and distant entry trojans like Agent Tesla, CyberGate RAT, Fenix botnet, Matanbuchus, NarniaRAT, Remcos RAT, Rhadamanthys, SapphireStealer, and zgRAT.
