

A financially motivated risk actor referred to as Magnet Goblin is swiftly adopting one-day safety vulnerabilities into its arsenal as a way to opportunistically breach edge gadgets and public-facing companies and deploy malware on compromised hosts.
“Risk actor group Magnet Goblin’s hallmark is its means to swiftly leverage newly disclosed vulnerabilities, significantly focusing on public-facing servers and edge gadgets,” Test Level stated.
“In some circumstances, the deployment of the exploits is inside 1 day after a [proof-of-concept] is revealed, considerably growing the risk degree posed by this actor.”
Assaults mounted by the adversary have leveraged unpatched Ivanti Join Safe VPN, Magento, Qlik Sense, and probably Apache ActiveMQ servers as an preliminary an infection vector to realize unauthorized entry. The group is claimed to be energetic since at the least January 2022.
A profitable exploitation is adopted by the deployment of a cross-platform distant entry trojan (RAT) dubbed Nerbian RAT, which was first disclosed by Proofpoint in Could 2022, in addition to its simplified variant referred to as MiniNerbian. The usage of the Linux model of Nerbian RAT was beforehand highlighted by Darktrace.
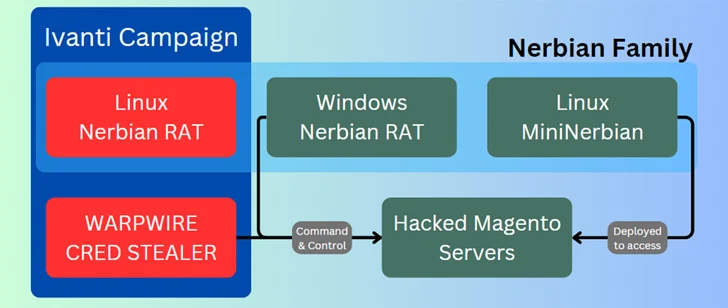
Each the strains permit for execution of arbitrary instructions acquired from a command-and-control (C2) server and exfiltrating the outcomes backed to it.
Among the different instruments utilized by Magnet Goblin embrace the WARPWIRE JavaScript credential stealer, the Go-based tunneling software program often known as Ligolo, and legit distant desktop choices reminiscent of AnyDesk and ScreenConnect.
“Magnet Goblin, whose campaigns seem like financially motivated, has been fast to undertake 1-day vulnerabilities to ship their customized Linux malware, Nerbian RAT and MiniNerbian,” the corporate stated.
“These instruments have operated underneath the radar as they largely reside on edge-devices. That is a part of an ongoing pattern for risk actors to focus on areas which till now have been left unprotected.”
